Cryptography | Free Full-Text | Power Side-Channel Attack Analysis: A Review of 20 Years of Study for the Layman
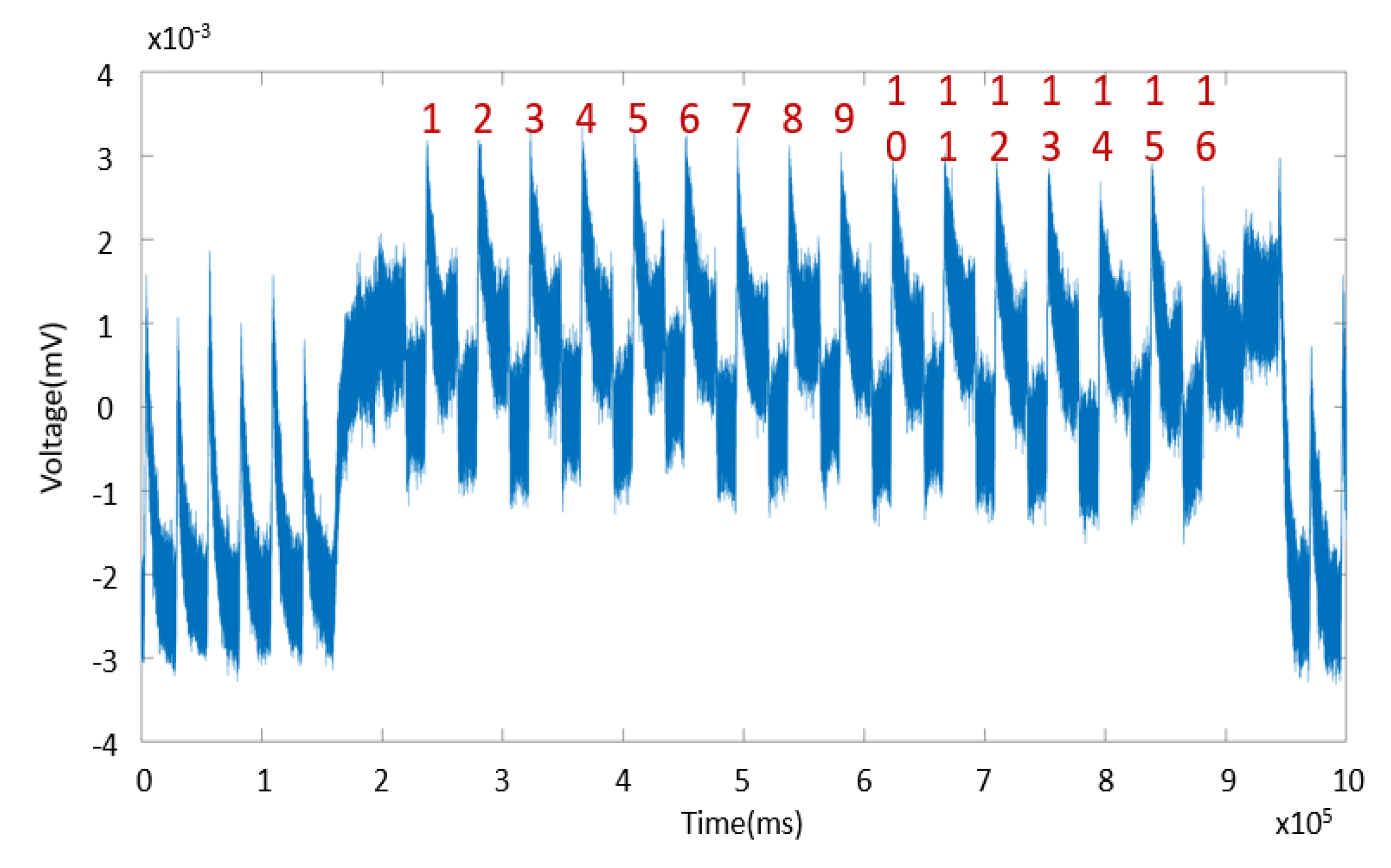
High Efficiency Power Side-Channel Attack Immunity using Noise Injection in Attenuated Signature Domain
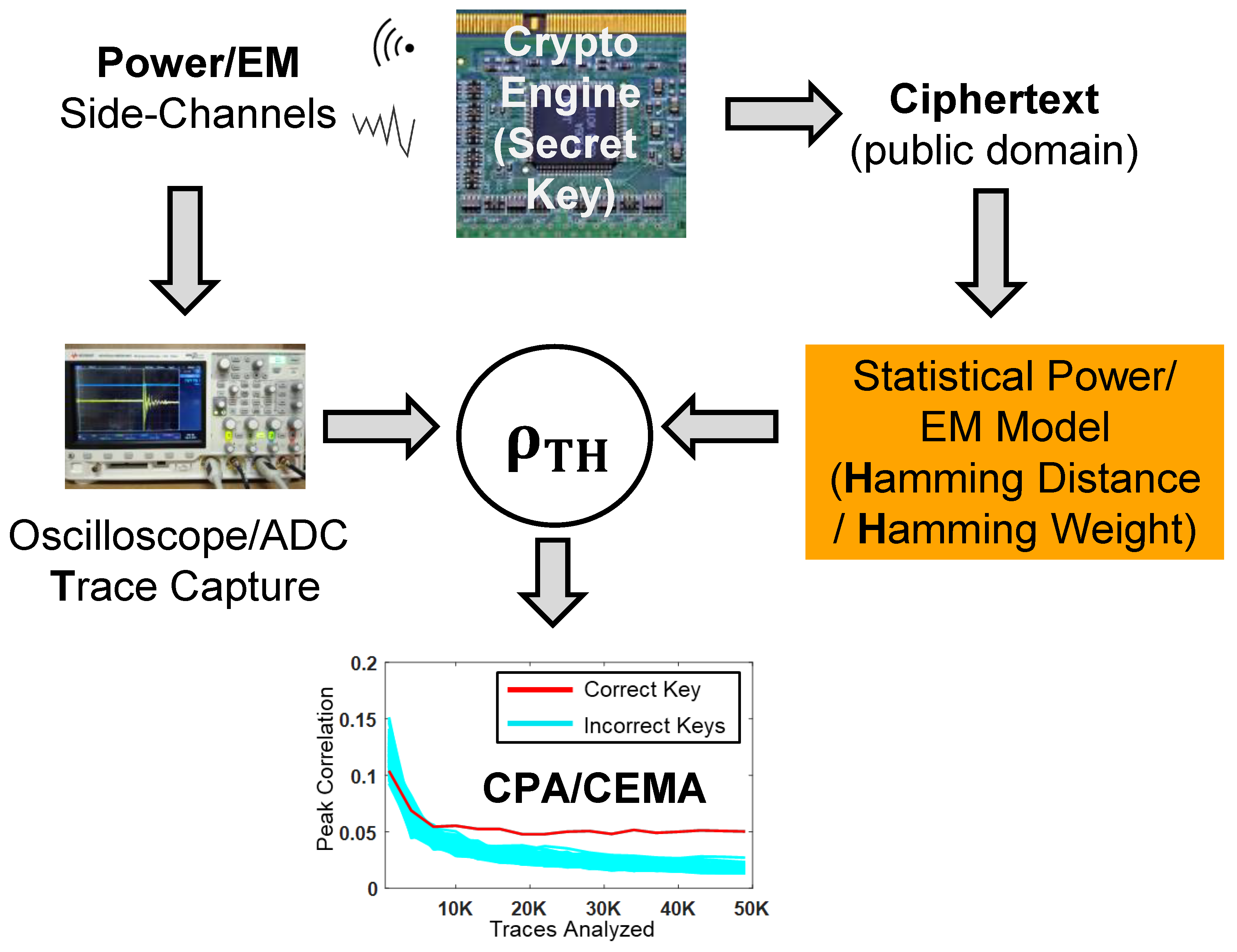
Cryptography | Free Full-Text | Electromagnetic and Power Side-Channel Analysis: Advanced Attacks and Low-Overhead Generic Countermeasures through White-Box Approach
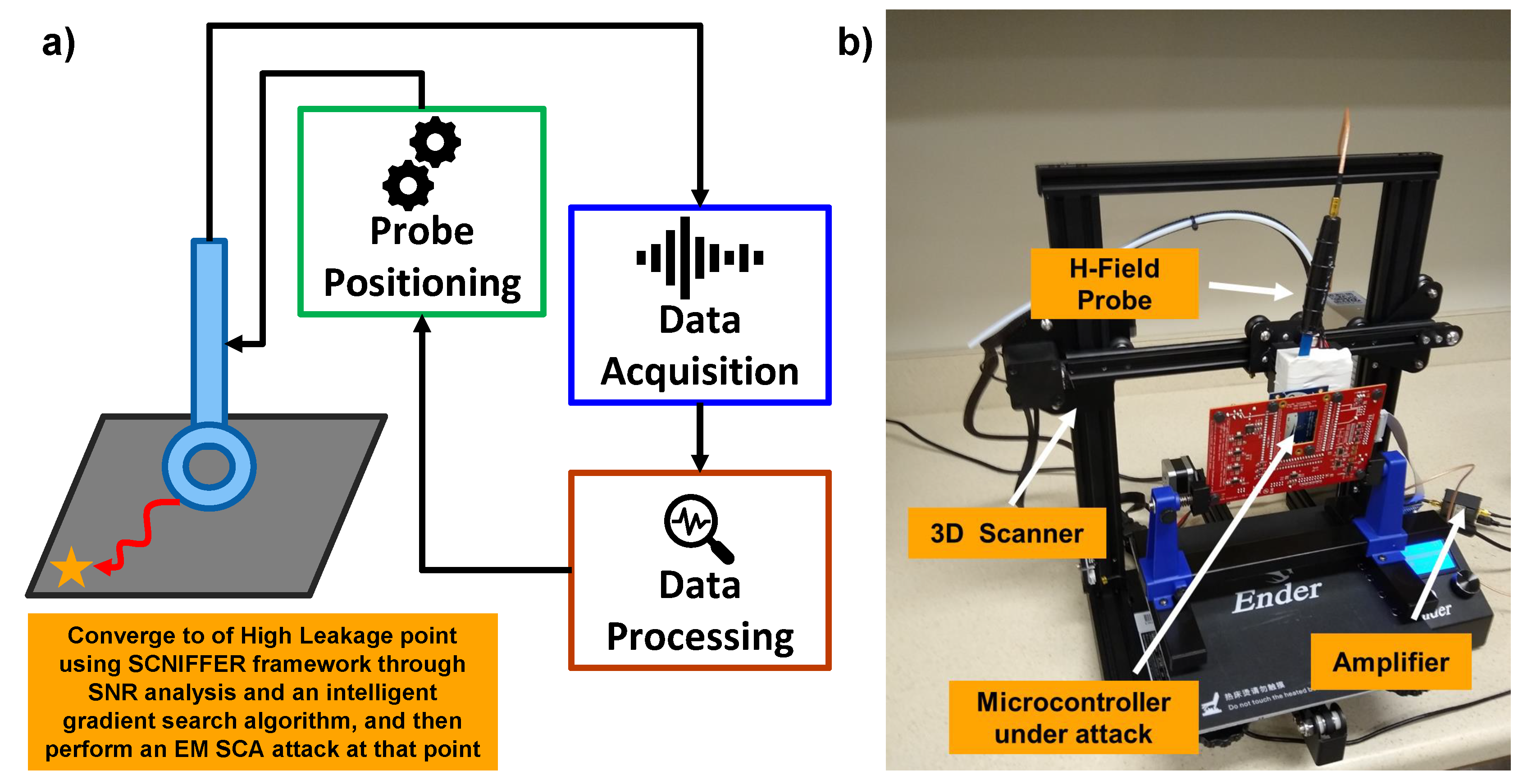
Cryptography | Free Full-Text | Electromagnetic and Power Side-Channel Analysis: Advanced Attacks and Low-Overhead Generic Countermeasures through White-Box Approach

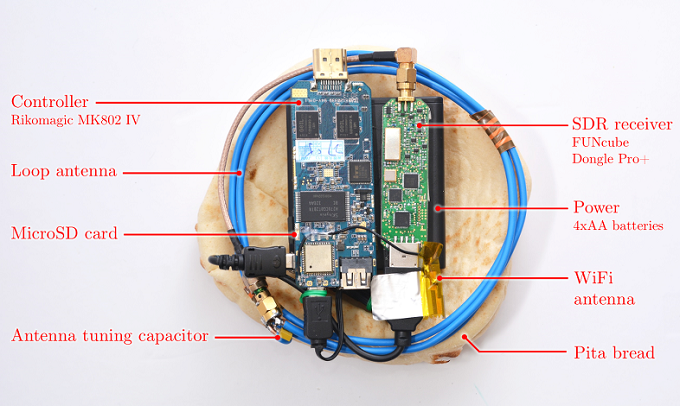
Leveraging Electromagnetic Side-Channel Analysis for the Investigation of IoT Devices - ScienceDirect